UNDERSTANDING CMMC 2.0
What is CMMC?
- The Department of Defense (DOD) Cybersecurity Maturity Model Certification (CMMC) is a unified cybersecurity standard designed to ensure protection of information in future DOD acquisitions. Specifically, it is focused on protecting and preventing unauthorized access to Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) within the DOD supply chain and Defense Industrial Base (DIB).
Are the number of levels changing with CMMC 2.0?
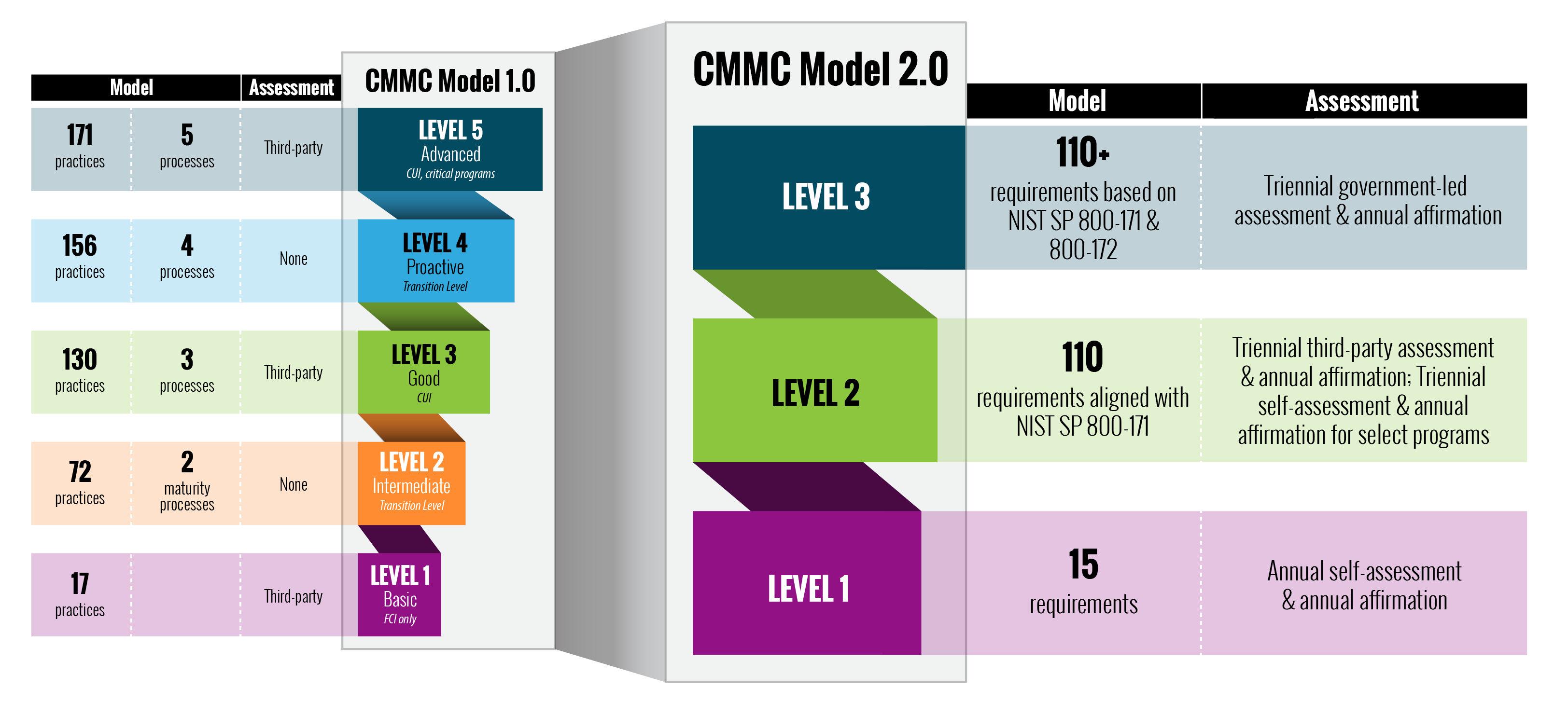
- Yes. What were formerly referred to as CMMC Level 2 and CMMC Level 4 no longer exist.
How did CMMC Level 1 change?
- CMMC Level 1 (if you only have FCI) will now only require an annual self-assessment (as opposed to an assessment by a CMMC Third-Party Assessment Organization (C3PAO)).
CMMC Level 3 is now CMMC Level 2? Did the underlying requirements change?
- Yes and yes. What was formerly CMMC Level 3 is now CMMC Level 2. The 20 unique CMMC controls/practices that were in addition to what is required in National Institute of Standards and Technology (NIST) Special Publication (SP) 800-171 and all 51 processes have been eliminated. Documentation is still required!
- The “new” CMMC Level 2 essentially equals NIST SP 800-171.
If I have CUI and am pursing the “new” CMMC Level 2, do I still need a third-party assessment from a C3PAO?
- It depends. The “new” CMMC Level 2 will be split into two paths:
1. Contracts that require an assessment from a C3PAO (every 3 years);
2. Contracts where an annual self-assessment and affirmation from company leadership will suffice. - The criteria determining the applicable CMMC Level 2 “path” have not been defined yet.
Does CMMC 2.0 change anything in regard to Plans of Action and Milestones (POA&Ms) and waivers?
- Yes. POA&Ms that are time-bound will be allowed (POA&Ms were previously not allowed).
- There will be certain controls within NIST SP 800-171/CMMC Level 2 that cannot be placed on a POA&M, and a minimum score will be required.
- Waivers to the CMMC requirement may be granted under certain limited circumstances (mission critical and requiring senior leadership approval).
What needs to happen for CMMC 2.0 to be effective in DOD contracts?
- The current CMMC piloting efforts (10-15 contracts were supposed to be the first to have a CMMC requirement) are suspended, and CMMC 2.0 will not be a contractual requirement until the DOD completes the rulemaking process to implement the program (can take 9-24 months).
- CMMC 2.0 will become a contractual requirement once rulemaking is completed.
- The DOD is exploring opportunities to provide incentives for contractors who voluntarily obtain a CMMC certification in the interim period. Additional information will be provided as it becomes available.
How will I know if CMMC applies to my contract(s)?
- Once CMMC 2.0 is implemented, the DOD will specify the required CMMC level in the solicitation and in any Requests for Information (RFIs), if utilized (same as CMMC 1.0).
Do prime contractors and subcontractors all need to be at the same level?
- If contractors and subcontractors are handling the same type of FCI and CUI, then the same CMMC level will apply. In cases where the prime contractor only flows down select information, a lower CMMC level may apply to the subcontractor (same as CMMC 1.0).
Any other key items I should be aware of?
- Under Defense Federal Acquisition Regulation Supplement (DFARS) 252.204-7012, contractors were expected to have implemented all 110 controls in NIST SP 800-171 no later than December 31, 2017.
- NIST SP 800-171/the “new” CMMC Level 2 still translates to 320 assessment objectives defense contractors need to accomplish.
- The False Claims Act (FCA) is still a very real enforcement mechanism, and the Department of Justice (DOJ) has already been taking a stronger stance regarding cyber violations.
How is Sawdey well-positioned to help your organization prepare for CMMC?
- We have a dedicated team of cybersecurity experts actively reviewing all CMMC developments.
- We are a Capability Maturity Model Integration for Services® (CMMI-SRV) Maturity Level 3 (ML3)-appraised company following International Organization for Standardization (ISO) 9001 certified processes.
- We have been selected by a major university as a partner responsible for educating suppliers on CMMC within the state of Ohio.
Specifically, what CMMC services can Sawdey provide your organization?
- Identification of the needed CMMC level, based on current DOD work, CUI being handled, and existing contract clauses.
- Pre-Assessment Gap Analysis – a comprehensive pre-assessment of your organization’s cybersecurity posture, identifying any deficiencies per NIST 800-171, CMMC, and DFARS requirements.
- Risk Mitigation Strategies – strategies to eliminate or reduce cybersecurity risks.
- Documentation/Deliverables – including, but not limited to, System Security Plan (SSP), POA&M, policies, plans, etc.
- Quality Analysis – additional assessment(s) to evaluate progress and address any outstanding POA&Ms.
- Assistance with uploading your self-assessment score in the Supplier Performance Risk System (SPRS).
- Education – initial and continuous guidance as DOD cybersecurity standards and policies evolve.
Prepare for CMMC with confidence.
Sawdey is helping DOD suppliers throughout the U.S. navigate the complexities of CMMC. To gain a competitive advantage in these evolving times, consider being proactive in taking the first step in preparation for CMMC 2.0. With Sawdey, you can achieve a high-quality pre-assessment of your current cybersecurity posture and learn how best to obtain your desired CMMC level in conjunction with your current and future business objectives.